CCNA 4 Final Exam V4.0 Answers Updated 2011 100%
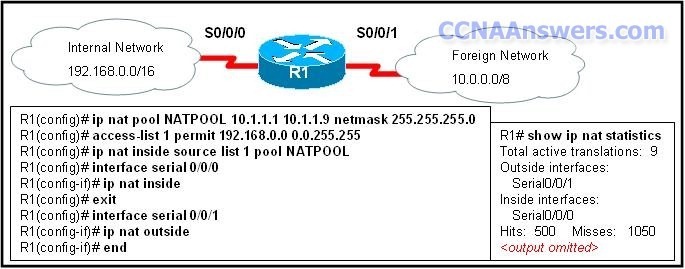
1. What functionality do access control lists provide in the implementation of dynamic NAT on a Cisco router?define which addresses can be translated
define which addresses are assigned to a NAT pool
define which addresses are allowed out the router
define which addresses can be accessed from the inside network
2. Which three guidelines would help contribute to creating a strong password policy? (Choose three.)
Once a good password is created, do not change it.
Deliberately misspell words when creating passwords.
Create passwords that are at least 8 characters in length.
Use combinations of upper case, lower case, and special characters.
Write passwords in locations that can be easily retrieved to avoid being locked out.
Use long words found in the dictionary to make passwords that are easy to remember. Read more »
Tags:
- Refer to the exhibit RIPv2 has been configured on all routers in the network Routers R1 and R3 have not received any RIP routing updates What will fix the issue?,acls final test answers,Which configuration on the vty lines provides the best security measure for network administrators to remotely access the core routers at headquarters?,ccna 2 v 4 0 final exam,Refer to the exhibit A network administrator configures a standard access control list on Router1 to prohibit traffic from the 192 168 0 0/24 network from reaching the Internet The access control list also permits traffic from the 192 168 0 0/24 network t,A network administrator configures a standard access control list on Router1 to prohibit traffic from the 192 168 0 0/24 network from reaching the Internet The access control list also permits traffic from the 192 168 0 0/24 network to reach the 192 168 1,ccna 4 practice final exam 1,ccna 4 final exam v4 0 answers,An issue of response time has recently arisen on an application server The new release of a software package has also been installed on the server The configuration of the network has changed recently To identify the problem individuals from both teams re,ccna 4 final exam answer
CCNA 4 Final answers (100% Guaranteed – Updated Dec 2010)
1. Which two statements are true about IPv6 link local addresses? (Choose two.)
They begin with the 2000::/3 prefix.
They begin with the FE80::/10 prefix.
They are assigned by IANA to an organization.
They must be manually configured by the administrator.
They are assigned to a host by a stateless autoconfiguration process.
2. Refer to the exhibit. What is another way to represent this IPv6 address?
2031::130F::9C0::130B
2031::130F::9C0:0:130B
2031:0:130F::9C0::130B
2031:0:130F::9C0:0:130B
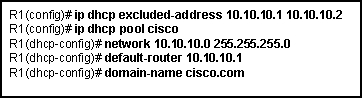
3. Refer to the exhibit. A host connected to Fa0/0 is unable to acquire an IP address from the DHCP server. The output of the debug ip dhcp server command shows “DHCPD: there is no address pool for 192.168.3.17″. What is the problem?
The address 192.168.3.17 address is already in use by Fa0/0.
The pool of addresses for the 192Network pool is configured incorrectly.
The ip helper-address command should be used on the Fa0/0 interface.
The 192.168.3.17 address has not been excluded from the 192Network pool.
4. What will be the result of adding the command ip dhcp excluded-address 10.10.4.1 10.10.4.5 to the configuration of a local router that has been configured as a DHCP server?
Traffic that is destined for 10.10.4.1 and 10.10.4.5 will be dropped by the router.
Traffic will not be routed from clients with addresses between 10.10.4.1 and 10.10.4.5.
The DHCP server will not issue the addresses ranging from 10.10.4.1 to 10.10.4.5.
The router will ignore all traffic that comes from the DHCP servers with addresses 10.10.4.1 and 10.10.4.5.
5. Refer to the exhibit. PC1, PC2, and PC3 are configured with dynamic address assignments. PC2 is assigned an IP address from the DHCP server. What would account for the IP addresses that are currently assigned to PC1 and PC3?
Switch S2 port Fa0/12 is configured for full-duplex.
These addresses were included in the DHCP server pools.
Router R1 has a misconfigured IP address on interface Fa1/0.
R1 interface Fa0/0 is not in the same network as the DHCP server.
R1 interfaces Fa0/0 and Fa1/0 do not include the ip helper-address command.
6. Refer to the exhibit. R1 is performing NAT overload for the 10.1.1.0/24 inside network. Host A has sent a packet to Web Server. What is the destination IP address of the return packet from Web Server when received at R1?
10.1.1.2:80
10.1.1.2:1234
172.30.20.1:1234
172.30.20.1:3333
7. Refer to the exhibit. Which configuration command would result in the output in the exhibit?
ip nat inside source static 10.1.200.254 172.16.76.3
ip nat inside source static 10.1.200.254 192.168.0.10
ip nat inside source static 172.16.76.3 10.1.200.254
ip nat inside source static 172.16.76.3 192.168.0.10
ip nat inside source static 192.168.0.10 172.16.76.3
ip nat inside source static 192.168.0.10 10.1.200.254
8. At what physical location does the responsibilty for a WAN connection change from the user to the service provider?
demilitarized zone (DMZ)
demarcation point
local loop
cloud
9. Which additional functionality is available on an interface when the encapsulation is changed from HDLC to PPP?
flow control
error control
authentication
synchronous communication
10. Which statement accurately describes a role that is played in establishing a WAN connection?
ISDN and ATM are circuit-switched technologies that are used to establish on demand a path through the service provider network.
Data link layer protocols like PPP and HDLC define how data is encapsulated for transmission across a WAN link.
A packet-switching network establishes a dedicated circuit between nodes for the duration of the communication session.
Frame Relay switches are normally considered to be customer premises equipment (CPE) and are maintained by local administrators.
11. Which data link layer encapsulation protocol is used by default for serial connections between two Cisco routers?
ATM
Frame Relay
HDLC
PPP
SDLC
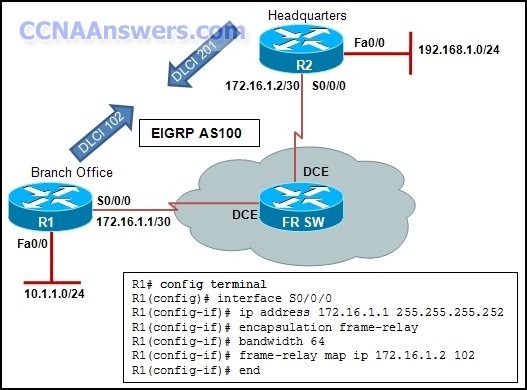
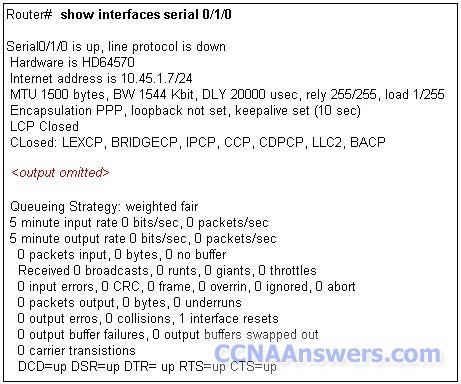
12. Refer to the exhibit. A network administrator is creating a prototype to verify the new WAN design. However, the communication between the two routers cannot be established. Based on the output of the commands, what can be done to solve the problem?
Replace the serial cable .
Replace the WIC on RA.
Configure RA with a clock rate command.
Issue a no shutdown interface command on RB.
13. Which protocol is used to authenticate connections over serial links securely?
CHAP
HDLC
SLIP
PAP
14. Which statement is true about PAP in the authentication of a PPP session?
PAP uses a two-way handshake.
The password is unique and random.
PAP conducts periodic password challenges.
PAP uses MD5 hashing to keep the password secure.
15. What is an accurate description of CHAP when used with PPP on a serial connection between two routers?
A username and password are sent to the peer router, which replies with an accept or reject message.
A username and password are sent to the peer router. If these match the configuration in the peer, the peer in turn provides a username and password to the initiating router.
A challenge message is sent to the peer router, which responds with its username and a calculated value based on a shared secret. This value is then compared by the challenger to its own calculations.
An encrypted password is sent to the peer router, which decrypts it and compares it to a shared secret. If the decrypted passwords match, the peer sends the encrypted password back to the initiating router.
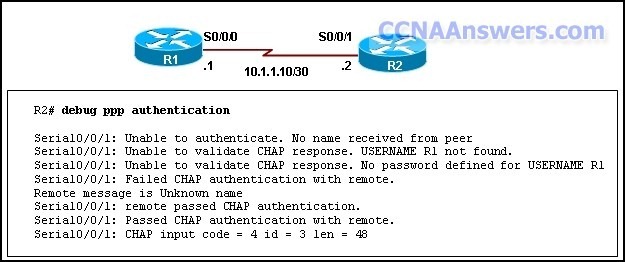
16. Refer to the exhibit. Communication between two peers has failed. Based on the output that is shown, what is the most likely cause?
interface reset
unplugged cable
improper LMI type
PPP negotiation failure
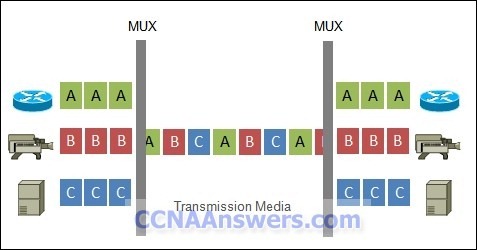
17. When configuring a Frame Relay connection, what is the purpose of Inverse ARP?
to assign a DLCI to a remote peer
to disable peer requests from determining local Layer 3 addresses
to negotiate LMI encapsulations between local and remote Frame Relay peers
to create a mapping of DLCI to Layer 3 addresses that belong to remote peers
18. A company is looking for a WAN solution to connect its headquarters site to four remote sites. What are two advantages that dedicated leased lines provide compared to a shared Frame Relay solution? (Choose two.)
reduced jitter
reduced costs
reduced latency
the ability to burst above guaranteed bandwidth
the ability to borrow unused bandwidth from the leased lines of other customers
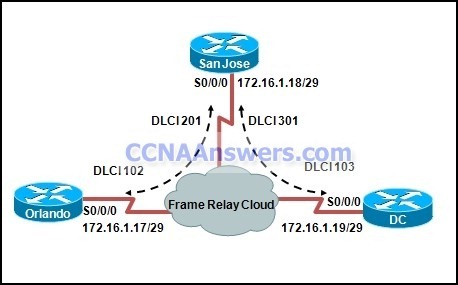
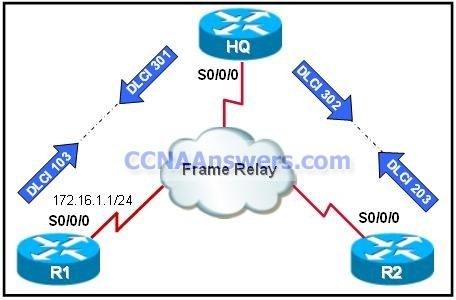
19. Refer to the exhibit. What is placed in the address field in the header of a frame that will travel from the San Jose router to the DC router?
DLCI 103
DLCI 301
172.16.1.18
172.16.1.19
20. Which option correctly defines the capacity through the local loop guaranteed to a customer by the service provider?
BE
DE
CIR
CBIR
21. When Frame Relay encapsulation is used, what feature provides flow control and exchanges information about the status of virtual circuits?
LCP
LMI
DLCI
Inverse ARP
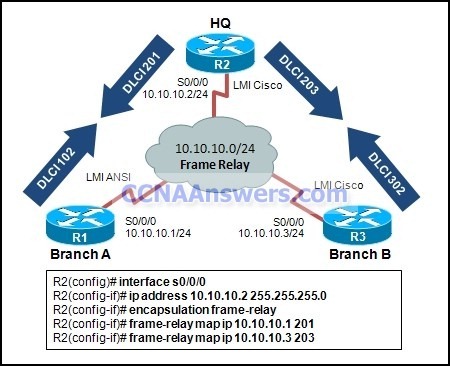
22. Refer to the exhibit. Branch A has a non-Cisco router that is using IETF encapsulation and Branch B has a Cisco router. After the commands that are shown are entered, R1 and R2 fail to establish the PVC. The R2 LMI is Cisco, and the R1 LMI is ANSI. The
LMI is successfully established at both locations. Why is the PVC failing?
The PVC to R1 must be point-to-point.
LMI types must match on each end of a PVC.
The frame relay PVCs cannot be established between Cisco and non-Cisco routers.
The IETF parameter is missing from the frame-relay map ip 10.10.10.1 201 command.
23. Refer to the exhibit. You are a network administrator who has been tasked with completing the Frame Relay topology that interconnects two remote sites. How should the point-to-point subinterfaces be configured on HQ to complete the topology?
HQ(config-subif)# frame-relay map ip 172.16.1.1 301 broadcast on Serial 0/0/0.1
HQ(config-subif)# frame-relay map ip 172.16.2.2 302 broadcast on Serial 0/0/0.2
HQ(config-subif)# frame-relay map ip 172.16.1.1 103 broadcast on Serial 0/0/0.1
HQ(config-subif)# frame-relay map ip 172.16.2.2 203 broadcast on Serial 0/0/0.2
HQ(config-subif)# frame-relay interface-dlci 103 on Serial 0/0/0.1
HQ(config-subif)# frame-relay interface-dlci 203 on Serial 0/0/0.2
HQ(config-subif)# frame-relay interface-dlci 301 on Serial 0/0/0.1
HQ(config-subif)# frame-relay interface-dlci 302 on Serial 0/0/0.2
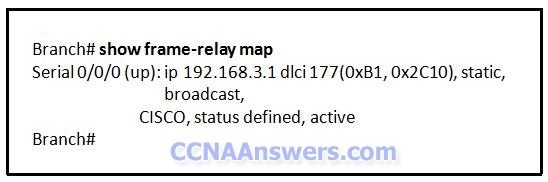
24. Refer to the exhibit. Which statement is true about the Frame Relay connection?
The Frame Relay connection is in the process of negotiation.
A congestion control mechanism is enabled on the Frame Relay connection.
The “ACTIVE” status of the Frame Relay connection indicates that the network is experiencing congestion.
Only control FECN and BECN bits are sent over the Frame Relay connection. No data traffic traverses the link.
25. Which IEEE 802.16 broadband wireless technology allows users to connect to the ISP at speeds comparable to DSL and cable?
Wi-Fi
satellite
WiMAX
Metro Ethernet
26. What are two main components of data confidentiality? (Choose two.)
checksum
digital certificates
encapsulation
encryption
hashing
27. Which statement about a VPN is true?
VPN link establishment and maintenance is provided by LCP.
DLCI addresses are used to identify each end of the VPN tunnel.
VPNs use virtual Layer 3 connections that are routed through the Internet.
Only IP packets can be encapsulated by a VPN for tunneling through the Internet.
28. From observing lots of port scans and ping sweeps on the company network, an administrator has determined that an edge router is experiencing an attack. These exploits are examples of what type of network attack?
DoS
access
reconnaissance
man-in-the-middle
29. A network administrator determines that falsified routing information is propagating through the network.
What action can be used to address this threat?
Update the IOS images.
Change console passwords.
Employ end-user authentication.
Configure routing protocol authentication.
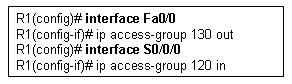
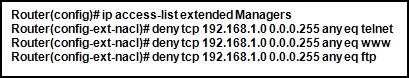
30. Refer to the exhibit. Which statement is true about the configuration of R1?
The remote session is encrypted.
A password is sent in plain text.
A connection that is using secure HTTP is enabled.
A local username database is used for authentication.
31. What can a network administrator do to recover from a lost router password?
use the copy tftp: flash: command
boot the router to bootROM mode and enter the b command to load the IOS manually
telnet from another router and issue the show running-config command to view the password
boot the router to ROM monitor mode and configure the router to ignore the startup configuration when it initializes
32. Refer to the exhibit. A network administrator is trying to backup the IOS software on R1 to the TFTP server. He receives the error message that is shown in the exhibit, and cannot ping the TFTP server from R1. What is an action that can help to isolate this problem?
Use correct source file name in the command.
Verify that the TFTP server software is running.
Make sure that there is enough room on the TFTP server for the backup.
Check that R1 has a route to the network where the TFTP server resides.
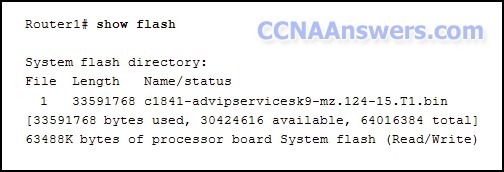
33. Refer to the exhibit. A network administrator is considering updating the IOS on Router1. What version of IOS is currently installed on Router1?
1
12.4
15
1841
34. Which statement is true about wildcard masks?
A wildcard mask must be created by inverting the subnet mask.
A wildcard mask performs the same function as a subnet mask.
A wildcard mask of 0.0.0.0 means the address should match exactly.
A wildcard mask uses a “1″ to identify IP address bits that must be checked.
35. Which type of ACL will permit traffic inbound into a private network only if an outbound session has already been established between the source and destination?
extended
reflexive
standard
time-based
36. Which variable is permitted or denied by a standard access control list?
protocol type
source IP address
source MAC address
destination IP address
destination MAC address
37. A technician is editing and reapplying ACL 115 to a router, what is the result of adding the command access-list 115 permit tcp any 172.16.0.0 0.0.255.255 established to the ACL when it is reapplied to the router?
All traffic that comes from 172.16.0.0/16 will be allowed.
All TCP traffic that is destined for 172.16.0.0/16 is permitted.
Any SYN packets that are sent to 172.16.0.0/16 will be permitted.
Responses to traffic that originates from the 172.16.0.0/16 network are allowed.
38. Refer to the exhibit. The network administrator creates a standard access control list to prohibit traffic from the 192.168.1.0/24 network from reaching the 192.168.2.0/24 network while still permitting Internet access for all networks. On which router interface and in which direction should it be applied?
interface Fa0/0, inbound
interface Fa0/0, outbound
interface Fa0/1, inbound
interface Fa0/1, outbound
39. Which option represents a best practice for applying ACLs?
Named ACLs are less efficient than numbered ACLs.
Standard ACLs should be applied inside the core layer.
ACLs applied to outbound interfaces use fewer router resources.
Extended ACLs should be applied closest to the source that is specified by the ACL.
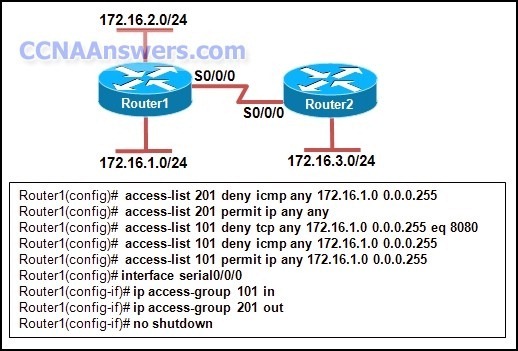
40. Refer to the exhibit. Which statement correctly describes how Router1 processes an FTP request packet that enters interface S0/0/0, and is destined for an FTP server at IP address 172.16.1.5?
The router matches the incoming packet to the statement that is created by access-list 201 permit ip any any command and allows the packet into the router.
The router reaches the end of ACL 101 without matching a condition and drops the packet because there is no statement that was created by access-list 101 permit ip any any command.
The router matches the incoming packet to the statement that was created by the access-list 101 permit ip any 172.16.1.0 0.0.0.255 command, ignores the remaining statements in ACL 101, and allows the packet into the router.
The router matches the incoming packet to the statement that was created by the access-list 201 deny icmp 172.16.1.0 0.0.0.255 any command, continues comparing the packet to the remaining statements in ACL 201 to ensure that no subsequent statements allow FTP, and then the router drops the packet.
41. A network administrator has moved the company intranet web server from a switch port to a dedicated router interface. How can the administrator determine how this change has affected performance and availability on the company intranet?
Conduct a performance test and compare with the baseline that was established previously.
Determine performance on the intranet by monitoring load times of company web pages from remote sites.
Interview departmental administrative assistants and determine if they think load time for web pages has improved.
Compare the hit counts on the company web server for the current week to the values that were recorded in previous weeks.
42. Technicians from Company A and Company B are comparing DSL transfer rates at their respective companies. Both companies are in the same city, use the same service provider, and have the same rate/service plan. Company A, however, reports higher download speeds than Company B. Which option best explains the reason for Company A having the higher download speeds?
Company A only uses microfilters on branch locations.
Company B has a higher volume of POTS voice traffic than does Company A.
Company B shares the connection to the DSLAM with a larger number of clients than Company A shares.
The length of the local loop between Company A and the CO is shorter than the length of the local loop between Company B and CO.
43. Which characteristic of VPN technology prevents the contents of data communications from being read by unauthorized parties?
QoS
latency
reliability
confidentiality
44. A recently patched application server is experiencing response time problems. The network on which the application server is located has been experiencing occasional outages that the network team believes may be related to recent routing changes. Network and application teams have been notified to work on their respective issues. Which statement applies to this situation?
Only results from the software package should be tested as the network is designed to accommodate the proposed software platform.
Scheduling will be easy if the network and software teams work independently.
It will be difficult to isolate the problem if two teams are implementing changes independently.
Results from changes will be easier to reconcile and document if each team works in isolation.
45. Because of a remote-procedure call failure, a user is unable to access an NFS server. At what layer of the TCP/IP model does this problem occur?
network layer
data link layer
physical layer
application layer
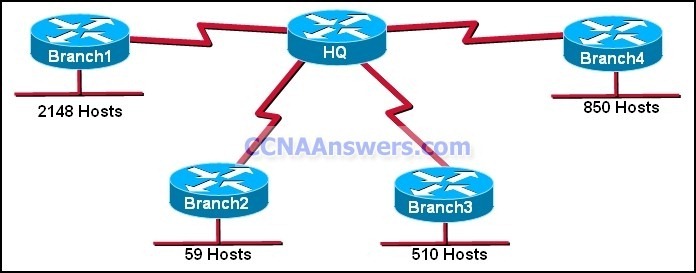
46. Refer to the exhibit. The corporate network that is shown has been assigned network 172.16.128.0/19 for use at branch office LANs. If VLSM is used, what mask should be used for addressing hosts at Branch4 with minimal waste from unused addresses?
/19
/20
/21
/22
/23
/24
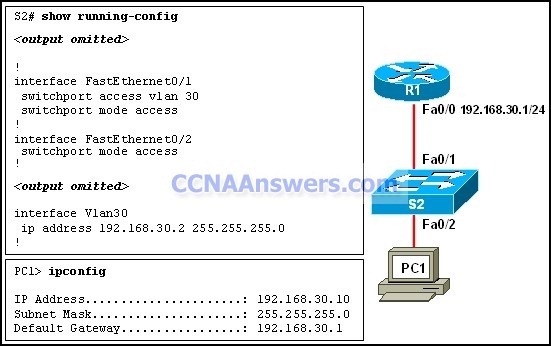
47. Refer to the exhibit. All devices are configured as shown in the exhibit. PC1 is unable to ping the default gateway. What is the cause of the problem?
The default gateway is in the wrong subnet.
STP has blocked the port that PC1 is connected to.
Port Fa0/2 on S2 is assigned to the wrong VLAN.
S2 has the wrong IP address assigned to the VLAN30 interface.
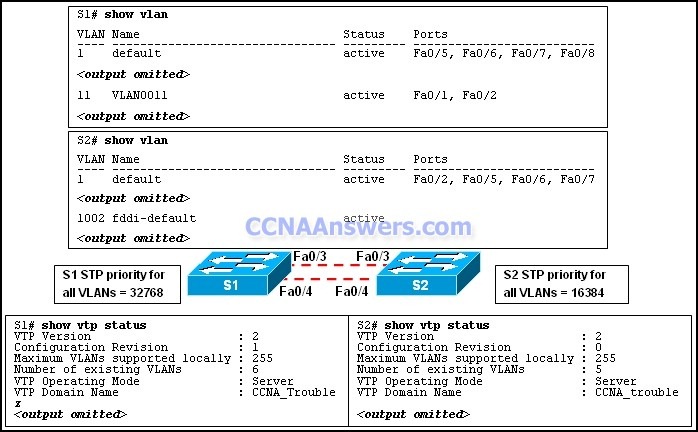
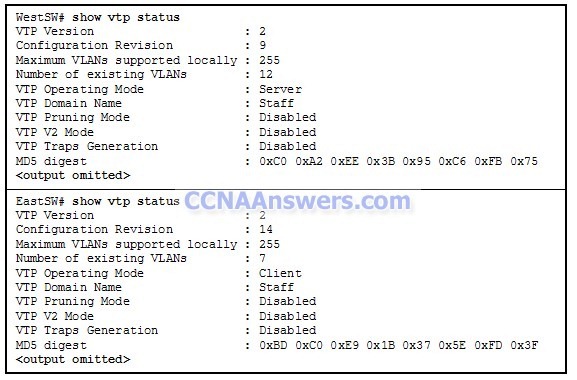
48. Refer to the exhibit. Results of the show vlan and show vtp status commands for switches S1 and S2 are displayed in the exhibit. VLAN 11 was created on S1. Why is VLAN 11 missing from S2?
There is a Layer 2 loop.
The VTP domain names do not match.
Only one switch can be in server mode.
S2 has a higher spanning-tree priority for VLAN 11 than S1 does.
49. Refer to the exhibit. Routers R1 and R2 have been configured with EIGRP in the same autonomous system. Computers PC1 and PC2 are not able to ping each other. Further investigation has revealed that the route to 192.168.10.0 is missing from the routing table on R2. What is the cause of the problem?
The networks are not correctly summarized.
The FastEthernet interfaces on R1 are configured as passive.
The network statements on R2 are incorrectly configured.
EIGRP on R1 does not recognize the 192.168.10.0 network.
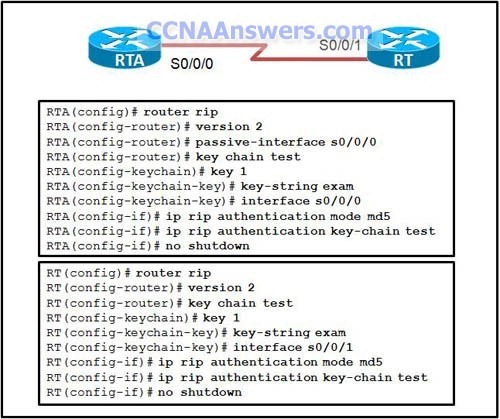
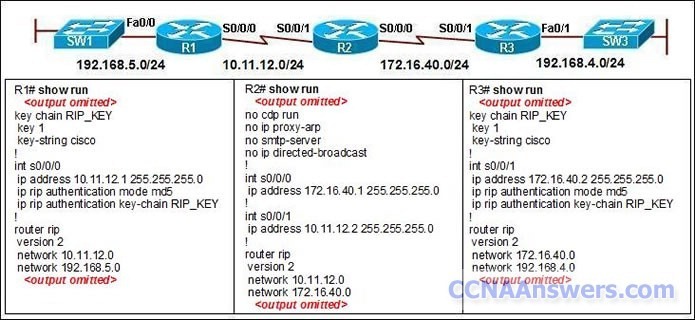
50. Refer to the exhibit. RIPv2 has been configured on all routers in the network. Routers R1 and R3 have not received any RIP routing updates. What will fix the issue?
Enable RIP authentication on R2.
Issue the ip directed-broadcast command on R2.
Change the subnet masks to 10.11.12.0/8 and 172.16.40.0/16 on R2.
Enable CDP on R2 so that the other routers will receive routing updates.